Now that public exploits are available for the DNS cache poisoning attack, now is good time to patch your DNS servers if you haven’t already.
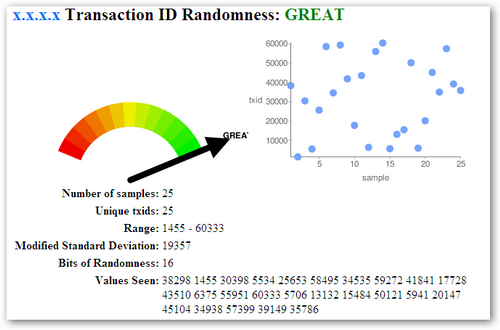
Some new tools also came out to test if your DNS server is vulnerable to DNS cache poisoning. The web-based DNS randomness test by DNS-OARC is very good, and it outputs pretty graphics. For those that like the command line, you can also use dig and nslookup with the DNS-OARC test.
$ dig @IP-of-GOOD +short porttest.dns-oarc.net TXT
$ nslookup -type=txt -timeout=30 porttest.dns-oarc.net IP-of-SERVER
Update: IBM’s Internet Security Systems blog has a good summary post called ‘Responding to the DNS vulnerability and attacks‘.
Update #2: Dan Kaminsky talked about the DNS vulnerability more in a Black Hat Webcast.
Related Link: Is Your DNS Server Vulnerable To Cache Poisoning?

Leave A Comment